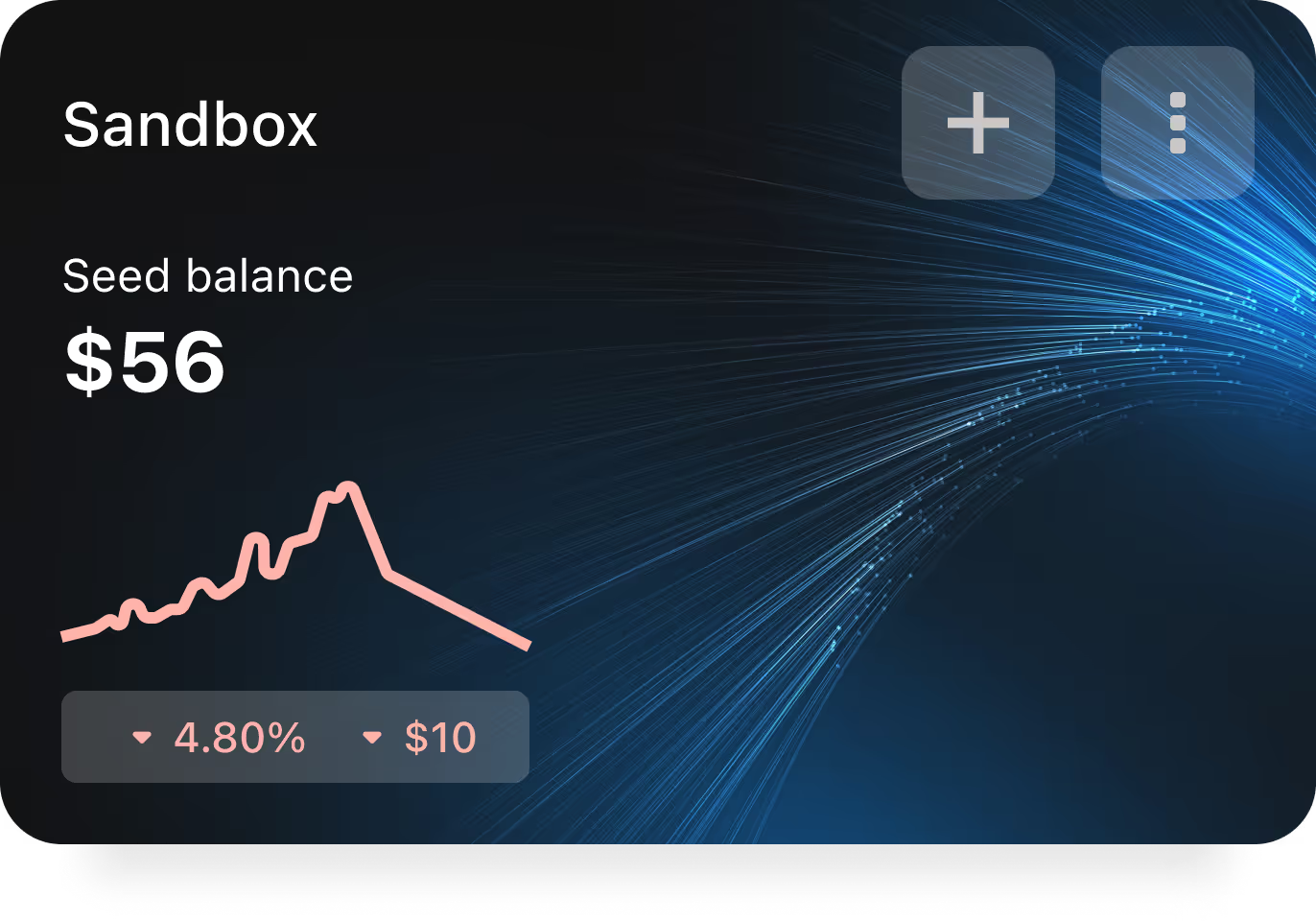
BUILT AS A SYSTEM,
NOT JUST A DEVICE
Security built into every layer.


RECOVERY PROCESS
Twice awarded by cybersecurity experts Decentralized & Anonymous.
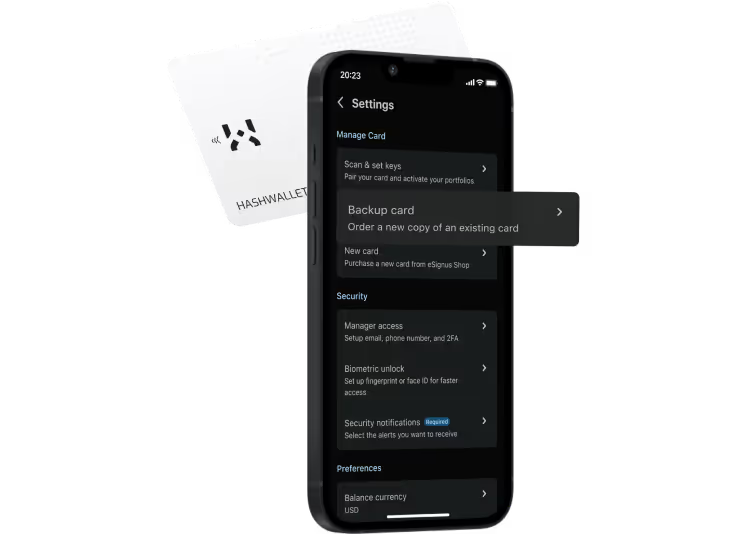
Receive a non-initialized card with your personal recovery seed.
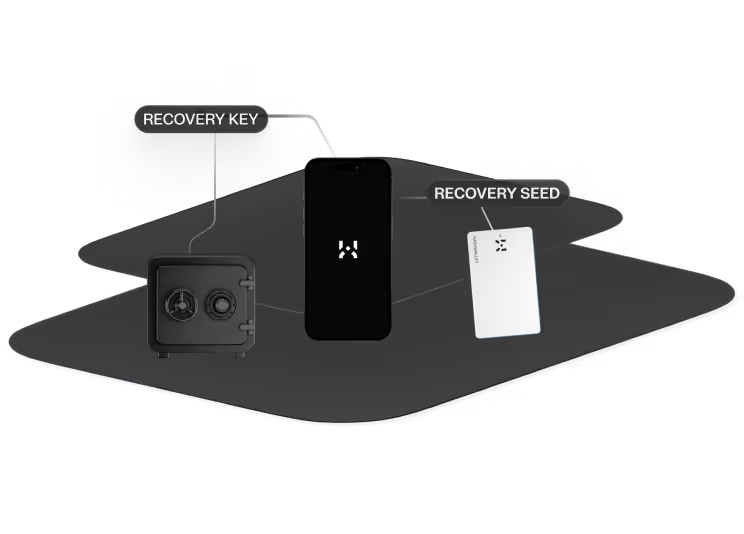
During the initialization, your recovery key is fetched from the Backup Center, and then stored and decrypted in your card's chip.

While scanning, your Recovery Seed and Recovery Key are processed to recompose your keys within the EAL6+ chip.

The Recovery Seed and Recovery Key aren’t your Private Key. With HASHWallet, your Keys stay securely stored within the chip and never leave it.

Your Private Keys are now stored in your EAL6+ chip. Offline and protected.
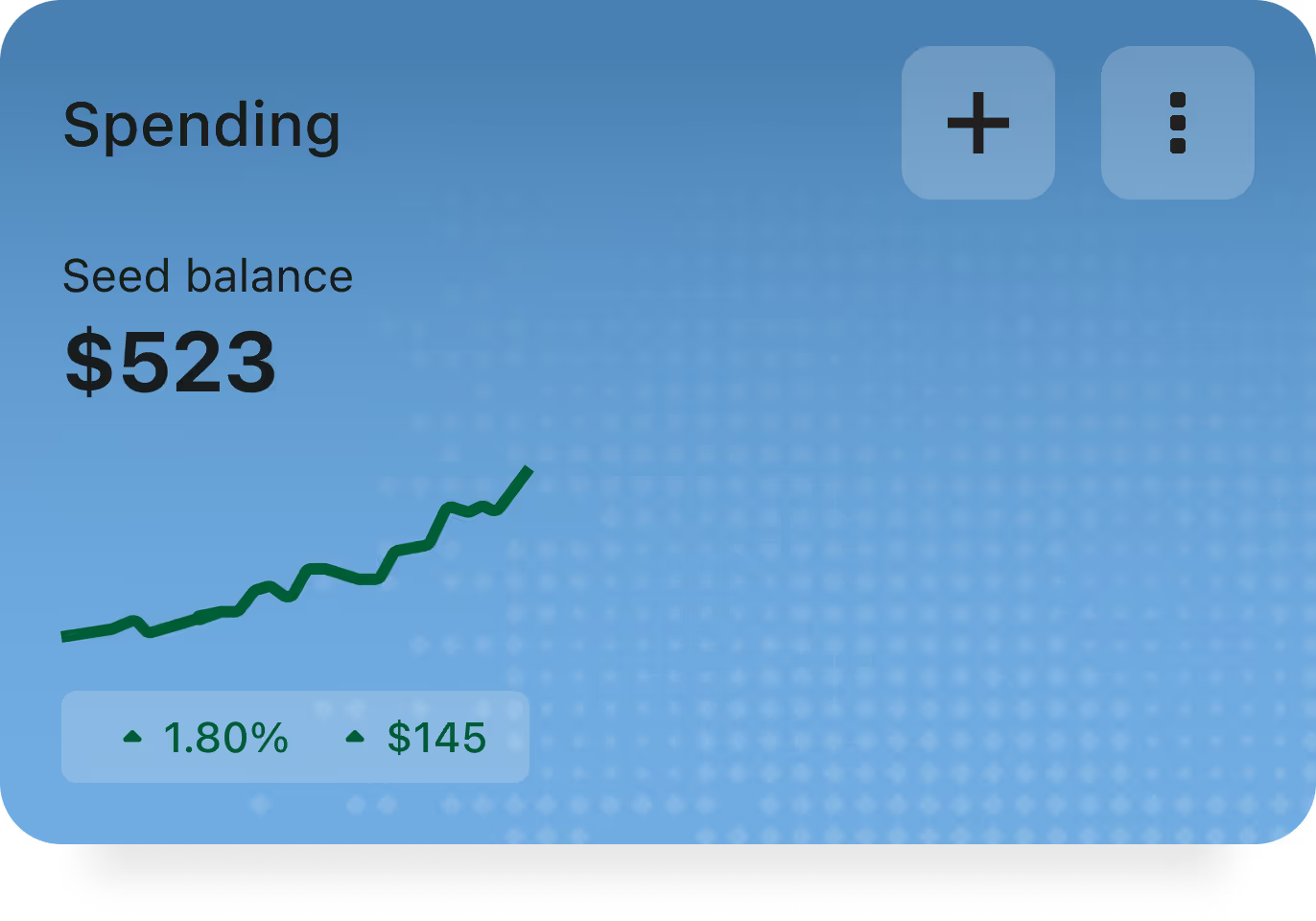
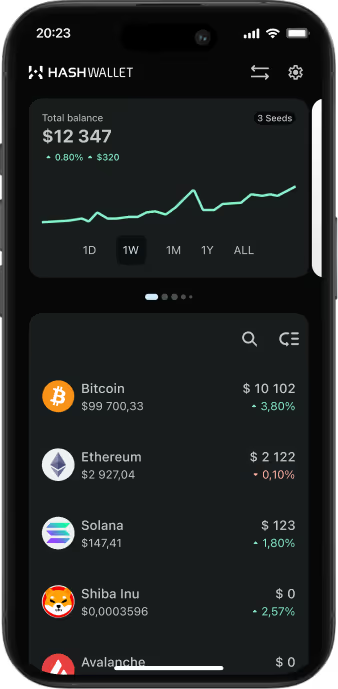
A card for them all
Secure all your private keys with a single card and keep them safe with HASHWallet’s multiple security layers.
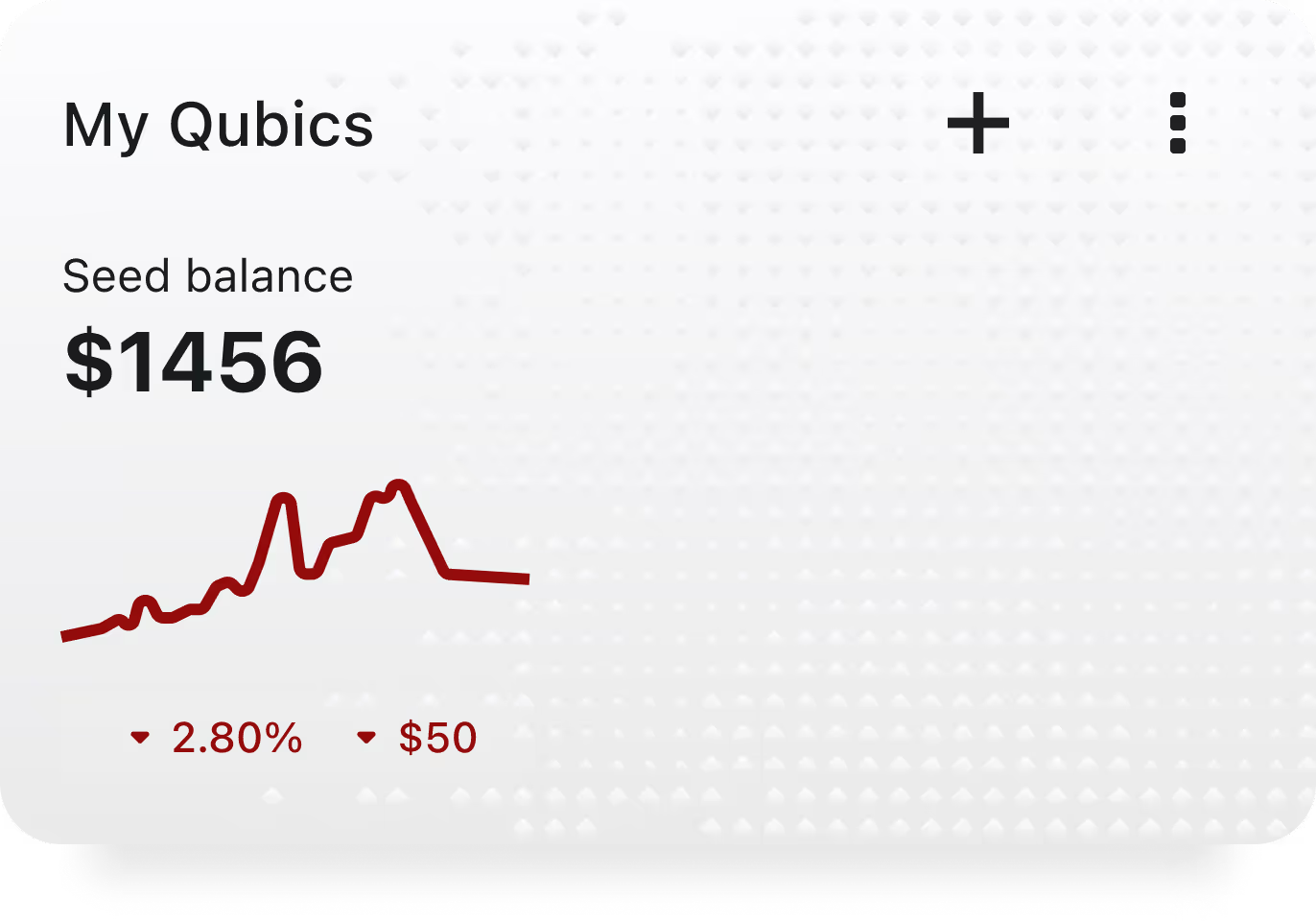
Multi-Seed Card
As many keys as needed
Never lose your keys again
SECURE INHERITANCE WITHOUT SHARING YOUR KEYS
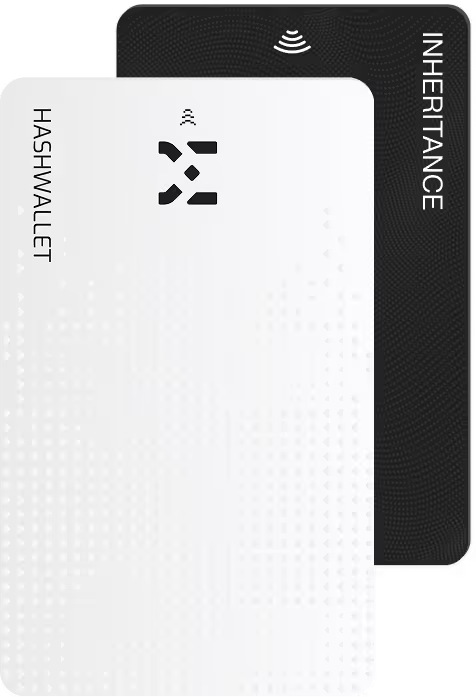
HASHWallet Elite
You're a step away from owning true
exclusivity

Frequently Asked Questions
No, you don’t. Buying a HASHWallet gives you free access to the recovery service for all your private keys. If you lose your HASHWallet card, all you need to do is order a new Backup Card from the app. There are no additional costs associated with the recovery process.
The HASHWallet non-updatable firmware avoids backdoors to your keys via malicious updates and also lacks commands for key extraction, adding an extra layer of security. New coins and features are added through application updates, which provides new functionalities without compromising your security.