FAQ
Yes, it is. With desktop and mobile wallets, your keys remain exposed to hackers, since they are stored in a device connected to the Internet. In contrast, HASHWallet securely stores your keys within the card's chip, keeping them offline and also protected by a system with multiple security layers designed to enhance key protection even more.
Exchanges are a primary target for hackers because they store massive amounts of cryptocurrency keys in centralized systems connected to the internet. This makes them highly vulnerable to large-scale breaches, as hackers can compromise thousands or even millions of accounts with a single attack.
In contrast, HASHWallet takes security to the next level. It securely stores your keys offline within the card’s secure chip, keeping them completely isolated from any internet connection. The HASHWallet system combines the advantages of cold wallets with additional layers of protection, making it significantly more secure.
Here’s the security hierarchy from most to least secure: HASHWallet → other cold wallets → mobile and desktop wallets → Exchanges
Your keys remain stored within the card’s chip that features the highest security certification on the market, EAL6+.
Although the system can help you regain access to your crypto anonymously, it does not store your keys anywhere outside the card’s chip. To restore access, the process relies on two elements, the Recovery Key and the Recovery Seed, neither of which contains your actual keys.
The HASHWallet non-updatable firmware avoids backdoors to your keys via malicious updates and also lacks commands for key extraction, adding an extra layer of security. New coins and features are added through application updates, which provides new functionalities without compromising your security.
No, you don’t. Buying a HASHWallet gives you free access to the recovery service for all your private keys. If you lose your HASHWallet card, all you need to do is order a new Backup Card from the app. There are no additional costs associated with the recovery process.
An updatable cold wallet can be compromised by injecting malicious firmware designed to expose your private keys. This is why HASHWallet was designed as a non-updatable cold wallet, eliminating the risk of firmware manipulation. To further enhance security, HASHWallet is engineered without any instructions to reveal private keys.
An attacker would need to know the exact email address associated with the account, gain access to either that email or the associated phone number to receive a verification code and enter the app, which shows an empty account with no balances or assets visible, without scanning the physical card. To see and manage any funds, the attacker would then need to order a backup card, which requires access to both email and phone to receive two verification codes, pay 95 euros for the card, and wait for it to arrive, all while the legitimate user may detect the attempt and recover access. No single element can be changed or recovered without the other two: changing the email address requires phone verification plus card scan; changing phone access requires email verification plus card scan; requesting a backup card requires both email and phone verification. The combination of cost, risk of being detected and neutralized, and uncertainty about the potential reward makes the attack impractical and economically unattractive.
No. The Backup Center stores a recovery element, the recovery key, which is not a private key, contains no part of it, and has no value on its own to access funds. Before being stored in the Backup Center, the recovery key and any other data are encrypted with the unique cryptographic scheme of the user's card. Each card uses a different encryption, so no two users share the same scheme.
Recovery is based on two independent elements that are not private keys and contain no part of them. The recovery seed is stored inside the user's card chip during manufacturing. The recovery key is stored in the user's personal Backup Center. Each element cannot be used on its own. Recovery can only be completed inside the chip of a new backup card, where the recovery key and recovery seed are processed together to regenerate private keys. The keys are never exposed outside the chip.
Access to the Backup Center is restricted to the user through their credentials, requiring the exact email address and verification codes sent to their email or phone. No third party can access it. All stored data is independently encrypted using the unique cryptographic scheme of each user's card, with no shared encryption between users. Even if the Backup Center were accessed and its contents decrypted, the stored data cannot be used on its own to access funds, meaning completing the attack provides no direct reward.
Only the user can initiate and complete recovery. The company has no access to the user's recovery elements. Even under legal request, the company has no technical means to recover a user's keys on their behalf.
Requesting a backup card only requires app credentials. Email and phone verification codes. No identity document, no personal verification, no third-party process.
The company does not hold the information needed for recovery. Without the user's access, recovery cannot be completed. The elements used for recovery, the recovery key, and the recovery seed, are not private keys; the keys are only ever reconstructed inside the chip. The company only helps users to carry out the recovery, but doesn't have access to it.
The Backup Center is a zero-knowledge vault built on HashiCorp Vault, a system specifically designed for secure secret storage rather than general-purpose servers.
HASHWallet uses a hierarchical deterministic wallet structure, generating multiple independent addresses from a single key. This prevents all activity from being linked to a single public address, reducing on-chain exposure and protecting financial privacy.
The chip firmware cannot be updated. This eliminates the risk of malicious firmware updates designed to extract keys, one of the most significant attack vectors in traditional hardware wallets. The firmware contains no commands to reveal or export keys, so key exportation is not possible by design. New coins, networks, and features are added through app updates, not firmware updates. The card doesn't need to be replaced to access new functionality. Bugs and issues are resolved through app updates.
No. Each card uses a different cryptographic scheme. Breaking the encryption of one card gives no access to any other. This makes mass attacks economically inefficient. Each user is a separate cryptographic target.
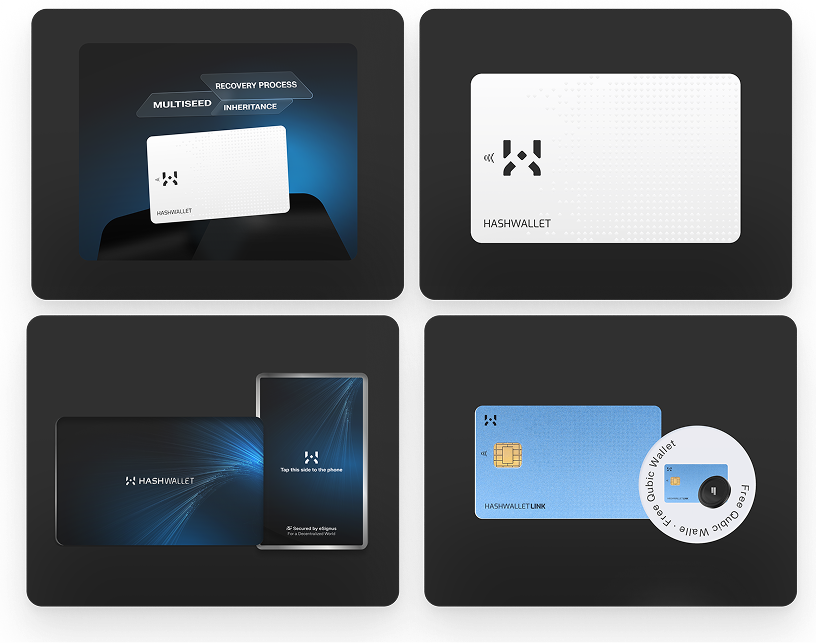
Users can organize inheritance of their digital assets without sharing private keys or credentials. A backup card can be requested and handed to an heir uninitialized. The email address associated with the account should be shared in the will, no password required.
When the time comes, the heir signs in with the decedent's email address and a phone verification code, then initializes the backup card.
Afterwards, they can change the email address to one of their own by verifying with card and phone OTP, then change the phone number using email verification and card scan.
An uninitialized card has no value and provides no access to funds. Keys are reconstructed inside the chip of the heir's card without ever being exposed.
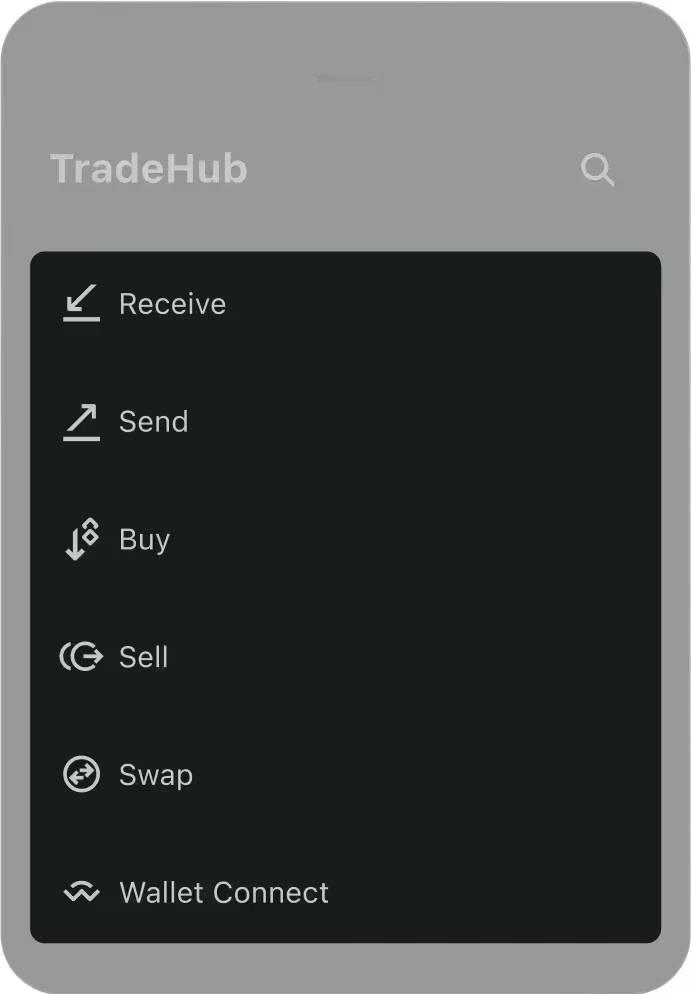
The app uses banking-grade security software provided by Build38, a mobile security company specialized in high-security apps for financial services and digital identity.
It continuously monitors the execution environment, detects rooted devices, manipulated apps, bots, and overlay attacks.
If the phone environment is not secure, the app stops functioning. It uses white-box cryptography, making reverse engineering or data extraction extremely difficult. Protection is active at all times, not only during signing.
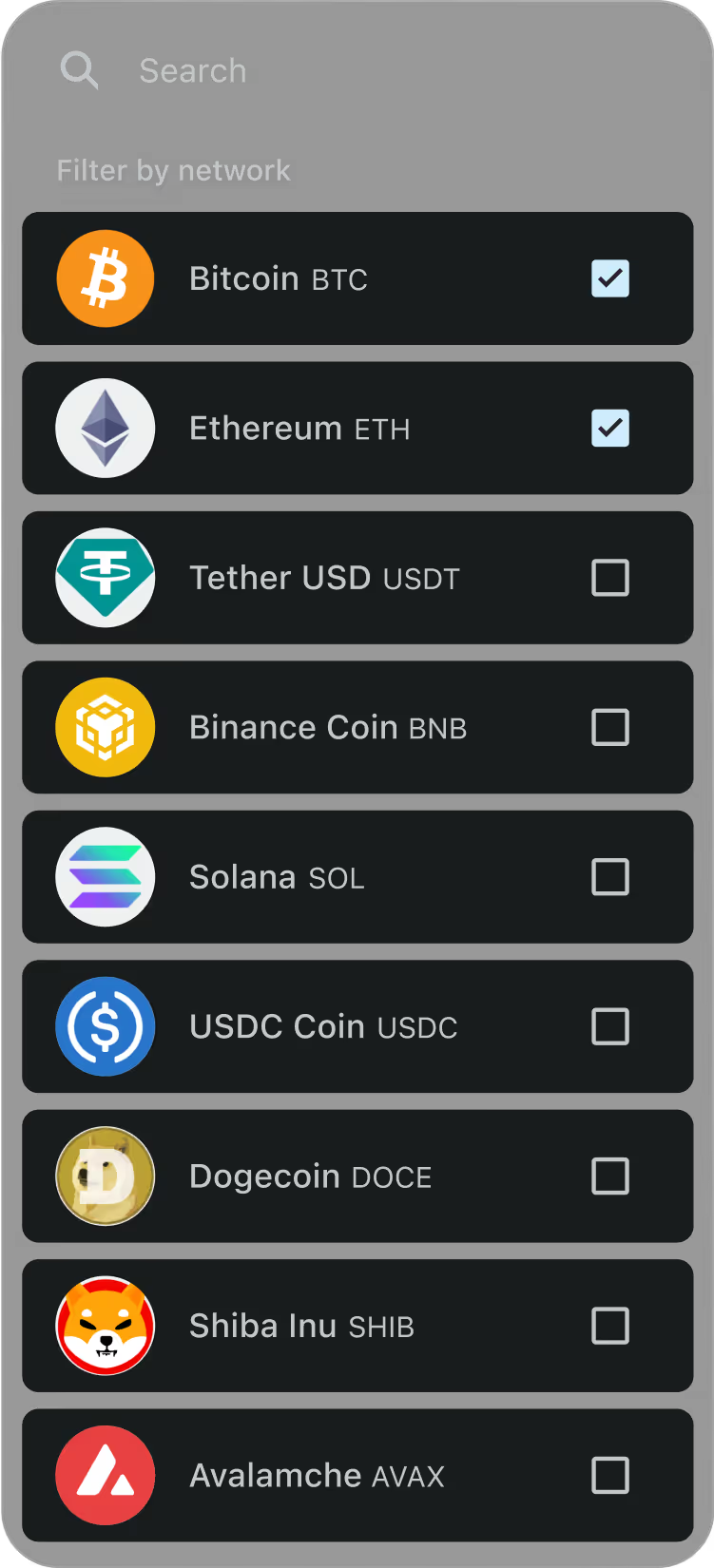
New coins, networks, and features are delivered through app updates. The physical card requires no replacement to support new functionality.
Most cold wallets are designed to manage a single private key. HASHWallet takes a different approach, allowing users to create or import multiple independent seeds on the same card, each completely isolated from the others.
Funds can be separated by use case, savings, daily spending, investments, or testing, improving both privacy and risk management.
If one key is used in a more exposed environment, the others remain secure. Also, a compromised key can be discarded and replaced with a new one without changing the card.
The main goal of the passphrase is to distribute key risk. It is generated and encrypted in the chip when the keys are created, then stored in the app. The user never sees it or memorizes it.
It is a security measure that happens in the background. Its purpose is to protect funds from any attack on the physical card. Even if the chip security were compromised, the attacker would find nothing of value, as the passphrase is necessary to complete the private keys.
Without app credentials, the card contents hold no value.
The secret passphrase does not interfere with using imported seed phrases on non-HASHWallet devices.
HASHWallet supports both options and they can be used simultaneously on the same card.
Users can generate seedless keys, created and stored inside the EAL6+ chip, never exposed to anyone, including the user and the company. There is no word list to write down, photograph, or steal.
Users can also import existing seed phrases into HASHWallet. Seedless-generated keys and imported seed phrases coexist on the same card, completely isolated from each other, and both benefit from the full recovery process, 100% self-custody, decentralized and anonymous.
HASHWallet is screenless and rather than a limitation, it is a different security approach.
Signing is 1-step and contactless via NFC. Security is established through a banking-grade app protection software secured by Build38, a mobile security company specialized in high-security apps for financial services and digital identity.
It continuously monitors the environment in real time: detects rooted devices, manipulated apps, and overlay attacks. Instead of relying on a physical screen that cannot verify whether the phone is compromised or a fake interface is active, HASHWallet addresses security at the environment level, providing broader protection.
Tangem's recovery process cannot truly be described as such, as it merely provides duplicates of the same wallet, which means that if all the cards are lost, the assets are irretrievable.
In contrast, HASHWallet allows users to order a Backup Card whenever needed, and initiate the recovery process. This ensures peace of mind, as funds remain securely protected even if cards get lost.
1. Anonymity
HASHWallet: Ensures full anonymity during recovery, requiring no personal information.Ledger Recover: Demands personal authentication to initiate the recovery process, potentially compromising user privacy.
2. Price
HASHWallet: Provides free recovery of all private keys just by ordering a new backup card whenever is needed.
Ledger Recover: Requires a paid monthly subscription for the recovery service of each private key, adding ongoing costs.
3. Key Management
Ledger Recover: Encrypts and splits keys into fragments stored with multiple custodians. While innovative, this introduces risks of compromise due to third-party involvement.
HASHWallet: Employs a secure recovery mechanism without storing private keys.
Recovery relies on two elements:
A Recovery Seed, stored offline in Hardware Security Modules (HSMs).
A Recovery Key, encrypted and stored in the Backup Center, accessible exclusively by the user.
We have created a decentralized recovery process that ensures only you can trigger it with access to your email and phone (via authentication codes). No one else, not even HASHWallet.
Although none of them are your private key, the system relies on two elements to enable the recovery process. A recovery seed stored within your backup card's chip, which has no value by itself. And, a recovery key, encrypted and stored in your Backup Center where only you can access the data with your credentials.
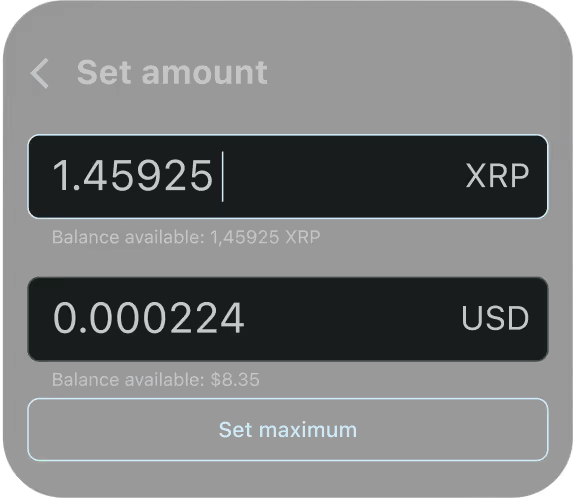
Buy HASHWallet

Qubic and all your assets in one single card.
€149
Benefit from our self custody recovery service whenever you need it, just by purchasing a backup card.
Instantly manage and switch between all your private keys from the app with your HASHWallet.
This advanced card supports Qubic tokens and over 11 000 crypto in other networks
86 x 54 mm (standard payment card size), temperature range from -13°F to +131°F, and IP68 water resistance.
HASHWallet Mobile App
All you expect from a cold wallet App and more


HASHWallet Elite
You're a step away from owning true
exclusivity